If you don’t where it is, you can’t protect it.
Do you know where ALL your organisation’s data is – not physically, but on which web and cloud services?
Here’s the problem. If you don’t where it is, then you can’t protect it. The secondary problem is finding out, because not everyone in your organisation will be onboard. It is common for people to sign up to web services because they offer something useful that helps them do their job.
They sign up using their email address and creating a password. There is the first headache – how does anyone track what has been signed up to across your organisation, let alone who has access to it? If that person leaves, no one will change the account credentials if they don’t know about it, but your ex-colleague still has access.
Secondly, what data do they upload? Is that data that you have a legal or moral responsibility for?
There’s nothing noble about Nobelium.
This isn’t theory – it’s real. USAID is a pretty important US organisation – promoting democracy and human rights around the world. Turns out, someone there was using a well-known email database tool called Constant Contact. But their account wasn’t well protected. Worse still, their account had a huge mailing set up, and of course, it had all the official USAID templates.
So, these Nobelium people, allegedly a Russian state-sponsored hacker group, compromised the Constant Contact account and sent a bulletin out. The bulletin contained malware that allowed the hackers to take command and control over victims computers. Ironically the fake email alleged interference in the US federal elections.

So, what can you do?
The first step is knowing what SaaS tools your people are using. We call this SHADOW IT and it is inevitable. Rather than stopping it, the job IT has is to identify it and manage it. The second step is to secure those platforms. That’s why our KARE for Security S2 plan contains a useful tool to help you identify what services your people are using.
Refer : What We Know About The Apparent Russian Hack Exploiting USAID : NPR
Real world Cyber-Security stories from the battlefront.
Every day we’re seeing more and more hacking attempts against clients. Cyber security attacks are getting more frequent, more threatening, and much more sophisticated. But for all that, and for all the associated risks, we’re astounded by the number of organisations...
Have you heard about “typosquatting”?
"Typosquatting" is the name given to criminals pretending to be someone they aren't - taking a domain name that uses a clever combination of legitimate-looking original sender email addresses, with spoofed display sender addresses that contain the target usernames and...
Preparing for a sudden Covid19 Delta Lockdown in New Zealand
Every week that we don't go into lockdown seems like a blessing. It can only be a matter of time before NZ is thrown back to a tight, restrictive lockdown. If, as we read yesterday, every Covid case coming in through the New Zealand border right now is infected with...
Cyber-war Seminar
Stories from the Cyber-war The simple reality is that cyber-crime is now a mega-business. The cost and effort to combat it grows all the time. "Is it worth it?" Good question. Every organisation needs to choose a level of security and resulting cost, effort and...
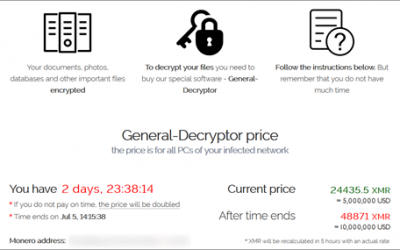
What you need to know about the massive global ransomware cyber-attack over the weekend
The Risk Is Real. Over the weekend, thousands of businesses were caught up in a global cyber-attack that is being blamed on a Russian hacker group called Revil. It is disappointing when geo-politics impacts everyday business, and the reports talk about President Biden...
(yet) another reason Why paying ransomware demands hurts. (The FBI agrees)
We don't negotiate with terrorists Recently, we asked the question if organisations should pay ransomware demands. There is a balance between desperation and the uneasy knowledge that you might be funding further criminal attacks on the community. We’ve just read a...
Pretending to be you or your colleagues
Just because it seems safe, doesn't mean it is. On some emails, you might see a warning that marks them as being ‘external’. This gets added as the email comes into your organisation. The idea is a simple one – if you see an email marked as external, then you will be...
Avoiding ad trackers when you browse the ‘net
Your own personalised stalker It always seemed slightly creepy that your computer shows advertising that is strangely accurately targeted at things you might have been interested in. On the surface, that seems quite useful. If you have to tolerate ads on your...
Phishing emails are getting smarter every day
In the old days (ie last year!!), a dodgy email had a whiff to it – there was something that triggered your subconscious. That’s because some phishing emails were really badly written with terrible English. But others just had a sniff about them- something that made...
A cyber-criminal only needs to get lucky once. You have to stay ahead of them all day, every day
"A cybercriminal only has to be lucky once, while a defender has to be lucky every minute of every day.” - Combating Ransomware - A Comprehensive Framework for Action: Key Recommendations from the Ransomware Task Force. The message we hear from governance boards over...